Top 7 Cybersecurity Threats Facing Small Businesses (and How to Stop Them)
Small businesses face an increasing number of cyberthreats that can interrupt operations and put company data at risk. From corrupt emails to ransomware, threat actors are consistently targeting small businesses because most aren’t employing advanced security measures, or don’t see themselves as a valuable target, making them easier to gain access to.
Having a robust cybersecurity plan for small businesses is no longer optional. It’s vital to safeguard your business, clients, and employees.
The good news is you don’t have to be a tech genius to make your business safe and secure.
With a couple of smart practices and help from a trusted provider of managed IT services in Santa Barbara, you can reduce your risk and stay one step ahead of cybercriminals.
Why Cybersecurity Matters for Small Businesses
Even small breaches can cripple a small business. A recent report from IBM stated that the average cost of a data breach for a small company (less than 500 employees) is more than three million dollars. Not only that, a cyber incident has losses beyond financial.
Reputation loss is an unknown cost. A cybercrime could mean the revelation of customer data or sensitive business information. After a breach, customers will often lose trust and have a high likelihood of abandoning a company. As a result, a small business will close its doors within months without recovery funding.
The rate of cyberattacks is high in today’s business landscape. Ransomware and phishing attacks are on the rise. Additionally, zero days and exploit kits have made vulnerability exploitation a common initial access vector.
That’s why it’s so critical for small business owners to enhance their cybersecurity strategies. Remaining informed about common cyberthreats improves your defenses and keeps your business secure.
Here are seven top cybersecurity threats for small businesses and how to protect yourself.
Top 7 Cybersecurity Threats to Small Businesses
#1 Phishing
Phishing is when scammers send fake emails that appear real, but are made to steal your login information, passwords, or financial details. A cyberthief aims to steal personal data such as:
- Social security numbers
- Passwords
- Bank and credit card information
These attacks usually happen via text messages or emails that seem trustworthy. Compromised emails and phishing can be ruinous for small businesses. Hackers typically make it appear as though a link or document is legitimate, which is harmful to the customers and the business. Businesses must have a cybersecurity plan in place, and everyone must be trained regarding cyberattacks.
Phishing continues to lead the cyberthreat world. Thieves are using more and more believable texts and emails to trick staff members into disclosing credentials or sending money. To avoid this:
- Never click on a questionable document or link. Check where it originated. Legitimate businesses usually don’t send emails or text messages from a Gmail, Yahoo, or Hotmail account.
- Always confirm payment requests via another method of communication (phone, in-person, etc.), even if they seem to come from a vendor or another team member.
- Use MFA (multi-factor authentication) whenever possible.
- Train your employees with security awareness programs that simulate phishing attacks and provide training so everyone in the company knows what to be on the lookout for.
#2 Weak Passwords
“Password” and “12345” are the most common passwords, and you should never use them. Furthermore, you should never use the same password for multiple accounts.
Stealing passwords is a continuing issue, and it’s vital to secure your accounts with clever, hard-to-guess password choices. Cyberthieves can use high-impact programs that test possible passwords fast. When a person uses personal information (child’s name, pet name, birthday, etc.) or common passwords, they don’t stand a chance against these attack methods.
Another method typically used by cyberthieves is called hashing. Based on the encryption strength of the account’s software, hackers can use a “hash”, a one-way encryption software, to steal passwords. To prevent cybercriminals from stealing your passwords:
- Use MFA on all accounts and require strong passwords
- Use password managers and identity management
- Scan server and cloud configurations often to avoid accidental exposure
- Use passphrases (a combination of unrelated words) for passwords (easier to remember; longer is better).
- For example: “PinkZebras Opened5Pistachios”
#3 Malware and Ransomware
Malware and ransomware are common forms of security threats for small businesses.
Malicious software (malware) denotes any code created to steal information, harm networks and computers, and gain unauthorized access to systems.
It usually comes from spam emails, linking to infected devices, or malicious website downloads.
Ransomware, an especially destructive type of malware, holds a business’s valuable, sensitive data captive, demanding a ransom for decoding. Often there is a threat of sharing the data publicly or deleting it permanently if the ransom is not paid.
Cyberthieves target small businesses, as they will usually pay the ransom due to insufficient backups and the vital need to resume operations, however even this is not a guarantee that your data will be returned safely. You can protect your business by:
- Frequently backing up your data to the cloud or an off-site location.
- Use dependable anti-malware and antivirus software.
- Training your staff about safe internet practices, including not opening suspicious emails or links.
#4 Data Breaches
Data breaches are a huge threat to small businesses. They happen when confidential and sensitive data is accessed, revealed to the public, or stolen.
This could occur because of a stolen or lost device, a phishing attack, or an employee’s mishandling of the company’s data.
Data breaches could lead to considerable damage to your reputation and revenue. Here are a few ways to protect your business:
- Encrypt your business data both at rest and in transit.
- Apply firm access controls to restrict who can handle and view confidential information.
- Routinely train employees on incident response processes and data protection best practices.
#5 Unpatched Systems and Software
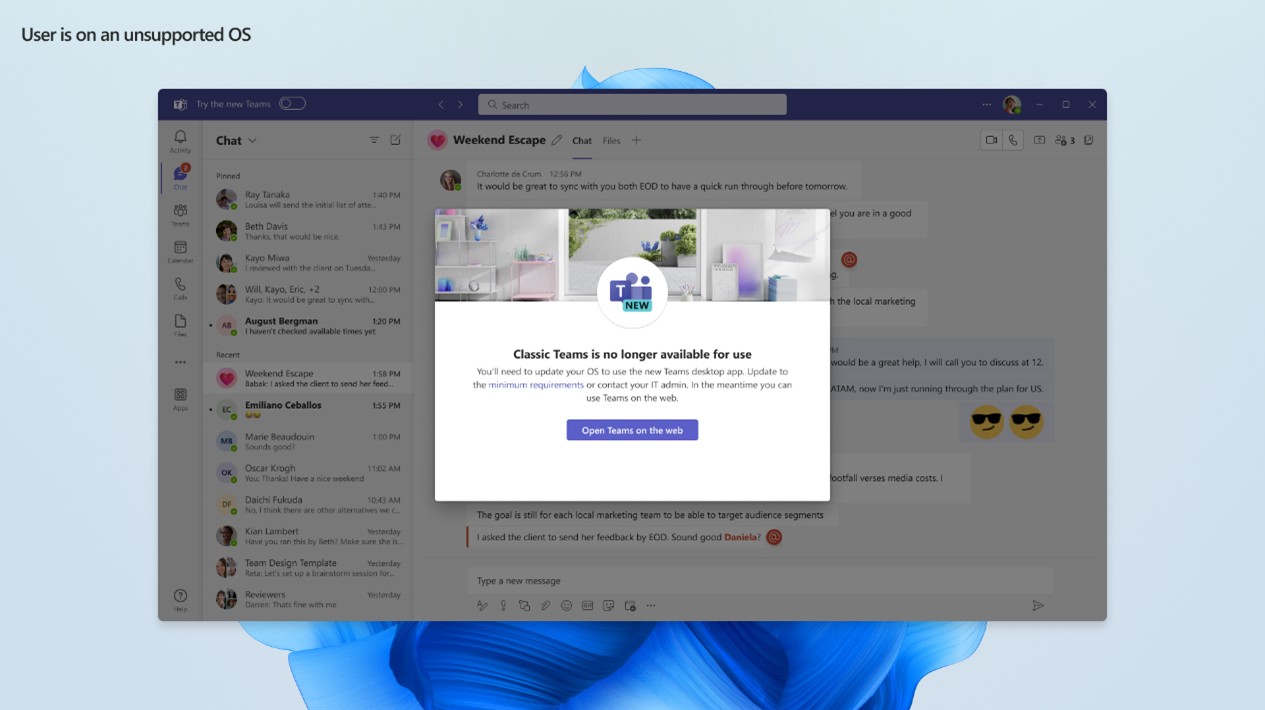
Small businesses typically put off updating operating systems and software because of time constraints or a lack of resources. However, using old versions leaves your business susceptible to cyberattacks.
Criminal hackers are professionals at detecting vulnerabilities in code, letting them slip viruses onto your devices. This is the reason why software companies are continually releasing updates with patches to seal these weaknesses.
Permit auto updates or engage an IT provider to apply patches weekly.
#6 Compromised Business Emails
A compromised business email is when attackers imitate a senior executive in your business or a vendor. Their goal is to deceive colleagues into transferring money or disclosing confidential data, like system passwords or banking information. A common situation is:
- An email that seems like it’s from a company executive or supervisor, but it’s fake.
- A request to transfer money immediately to a bank account with a credible reason as to why it’s urgent (for instance, to pay a new vendor).
- Getting an email deliberately at a busy time, such as the end of a quarter, and careful attention can’t be paid to it.
- An employee acts without thinking and sends money to a fake supplier without checking the invoice in the email.
Cyberattacks are extremely targeted and believable. Moreover, because of their low-tech nature, they usually bypass customary security tools.
To avoid being deceived by a compromised business email, tell employees to always double-check an email address from a person or business that is unfamiliar to them. It is also a good idea to make a quick call to be sure it is legit. Tell your employees that it’s better to be safe than sorry.
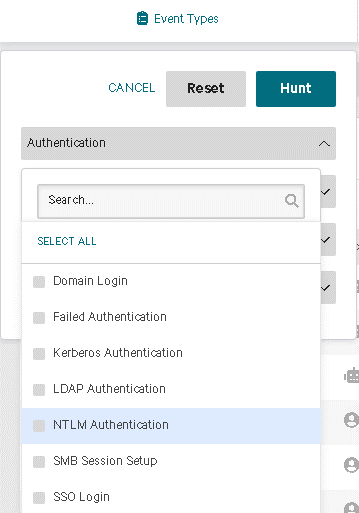
#7 Insider Risks
Cyberthreats can also come from within a business. Insider risks refer to possible security incidents or data breaches caused by contractors, employees, or others with valid access to your business’s data and systems.
These dangers typically arise from slips in judgment or inadvertent mistakes. For instance, an employee could accidentally mismanage sensitive data or give their login information to an unauthorized person, ignorant of the possible security repercussions.
Or an employee may unintentionally disclose your business data by not adhering to accurate security protocols or becoming a victim of a phishing attack. To protect your business:
- Encourage a culture of security awareness within your business.
- Perform routine cybersecurity training for every employee.
- Execute rigorous access controls and check user activities.
Cybersecurity Tips for Every Small Business
Think of these as cybersecurity tips to keep your small business safe and healthy:
Use strong, unique passwords – Establish complex passwords and don’t use them on more than one site. Consider using a password manager to keep them secure.
Update systems and software – Be sure to keep your anti-virus software updated. Routinely install updates and security patches.
Back up data frequently – Program backups to operate automatically. Store backups in a separate, safe place such as an external drive or the cloud.
Secure your Wi-Fi network – Have Wi-Fi for staff only and Wi-Fi for clients and visitors. Use a strong password for your router.
Train your employees – Be sure employees know how to detect and report suspicious activity. Human error is the cause of many cyber incidents, so training your employees is critically important.
The Bottom Line
Small businesses face an increasingly hostile environment of cybersecurity threats. However, with best practices such as employee training, routine updates, and strong passwords, they could significantly lessen any risks.
At CIO Solutions, we specialize in helping small businesses improve their security posture with full-service IT management or co-managed IT. As part of our managed service offerings, we provide access to an employee security awareness training program, advanced security solutions (EDR-endpoint detection and response solution), routine patching for security updates on managed endpoints, strategic guidance to ensure you’re covering your security bases, and more. Our team functions as both your fully managed IT provider and your trusted security partner.
If you’re ready to secure your business from today’s top cyberthreats, get in touch with us today, and let’s create security strategies customized to your needs.